SSL certificates
This article is a guide to SSL certificates (HTTPS) – what they are, how they work, and how to implement one on your website to protect your visitors.
Not HTTPS? You could be losing business
If your website is not HTTPS, then you face a couple of serious problems which means you might lose business:
- Google gives a small ranking boost to secure websites over non-secure ones – are your competitors’ websites HTTPS and yours not?
- Web browsers now show visitors an “insecure” warning when they use a website that is not HTTPS – what if they get spooked and leave?
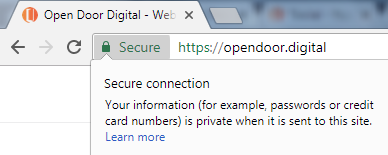
SSL (secure sockets layer) is a method of sending data securely between a user’s web browser and the website they are using. SSL is enabled by the web developer or website host through the installation of a security certificate. It protects sensitive information, such as passwords or credit card details, from being intercepted by a third party. A connection is secure when the website URL starts https:// and the web browser confirms the security certificate is trusted and has not expired.
When a connection is not secure, data exchanged between a user and a website is sent in clear view (unencrypted). This means a third party (a hacker) could eavesdrop on the line and see what is being exchanged (also known as a man-in-the-middle attack). If the user is simply browsing a website without any interaction, this is not a particular problem. However, if the user is typing in a password, filling in a contact form, or typing in credit card details, this is obviously a concern.
Internet networks are generally secure, meaning eavesdropping is not routine. However, internet traffic is routed through many different networks, owned by many different companies, in many different countries. Standards of security vary and the network is only as secure as its weakest link. Eavesdropping does happen which is why sending data securely is so important – even if it is intercepted it cannot be decrypted and abused.
Is https a legal requirement?
In the UK, a secure website connection is not a legal requirement. However, a secure connection is a mandatory part of PCI compliance (a set of rules that ensure safety of bank and card details). If a website is collecting sensitive financial information such as bank account or credit card numbers, a secure connection is mandatory. Failure to comply can lead to the withdrawal of transactional capabilities by banks, and where loss has occured because of poor security, the merchant can be held liable for fines and losses.
Many ecommerce websites use third party payment gateways to take card payments – such as PayPal or Worldpay – in those cases PCI compliance is the responsibility of the gateway, although it would still be unwise not to have a secure connection as the website will still be collecting other personal details such as name, address and so on.
SEO benefits of https
Google says it gives a ranking boost to websites that are secure:
we’re starting to use HTTPS as a ranking signal
Source: Google Webmaster Central Blog – https as a ranking signal
Non-secure sites trigger browser warning notices
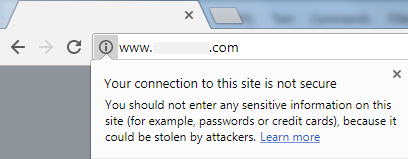
Modern web browsers show a discreet warning notice (seen when clicking the “i” icon) if a website is not secure:
However, if your visitor starts completing a contact form, a more worrying “Not Secure” notice appears in plain sight:
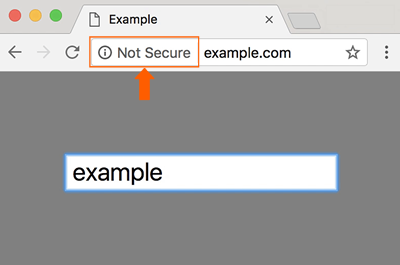
And, from July 2018, Chrome will permanently display the “Not Secure” warning during the whole visitor session, regardless of whether they complete a contact form. This does not inspire customer confidence and they might abandon their visit.
How SSL works
This section is written in very basic terms to aid understanding. For a detailed technical explanation, see the Wikipedia article on transport layer security.
When a connection between a user’s web browser and a secure website is first made, before any data is exchanged the website sends the user’s web browser a public key. This is a text file containing a unique combination of over one thousand characters that is used as a formula to encrypt data sent from the user to the website.
Crucially, the public key provides one-way encryption, which means the public key itself cannot decrypt the data it encrypted. This is important because an eavesdropper could have intercepted the public key (when it was first sent to the user) and the encrypted data being sent back – but they would not be able to decrypt that data with the public key.
The website itself has a private key, another unique combination of over one thousand characters, so called because it is never sent over the internet so cannot be intercepted. When the encrypted data is received by the website, the private key is able to decrypt the data.
Every website’s public and private key codes are unique to it, and can only be used a pair. The private key can only decrypt data sent from its own public key.
Could an eavesdropper guess the private key and decrypt the data?
In theory, yes; in practice, no. It can be considered impossible and that’s why banks are OK with online transactions.
As a private key is over one thousand random characters long, there is a mind boggling number of possible combinations. It would take a fast super-computer years to generate and test random sequences to hit on the exact code. This process would simply be too costly, lengthy, and unlikely to succeed for anyone to bother. And there would be no way of knowing what data was going to be uncovered anyway; it would more likely be innocent website traffic than usable financial information.
How to obtain an SSL certificate
SSL certificates can only be issued by trusted, audited certificate authorities (CA). There are only a handful of certificate authorities worldwide, however there are several thousand resellers of their services.
Process for obtaining an SSL certificate
This is not really for the layman but it’s a simple process for a web designer or developer:
- create a certificate signing request (CSR) on the website’s server – this creates the public and private keys unique to that web server (the hosting company can assist with this)
- purchase the SSL certificate from a CA
- the CA will request the public key – never give them the private key
- the CA will seek confirmation that the person buying the certificate controls the website in question, for example asking for a verification code to be added to the website
- the CA will then create the SSL certificate based on the public key; it takes the form of a small file that is installed on the website’s server (the hosting company can assist with this)
Price of an SSL certificate
Basic certificates are cheap to buy (if you shop around). A typical price is around £10 / year. Some web hosting companies offer them for free. Other types of certificates are more expensive (£100 or more) due to the manual identity checks needed.
Types of SSL certificates
There are three types of SSL certificate. What differs is the proof of identity checks the website owner has to go through before the certificate is issued.
Domain validated certificates (DV SSL)
This is the easiest type of certificate to obtain. The website owner simply has to prove that they control the website they have asked to be secured. They can prove this by adding validation code to their website, or by replying to an email sent to an @theirwebsite.co.uk email address. There are no identity checks of the individual or organisation making the request. This type of certificate is for encryption only and is not proof that the person or organisation receiving the data is who they say they are. Therefore, this type of certificate is not suitable for high risk data such as online banking or the input of credit card numbers.
DV SSL certificates are issued more or less instantly, as the process is automated.
Organisation validated certificates (OV SSL)
With an OV SSL, before the certificate is issued, the CA carry out checks that the organisation name given in the application did indeed make the request, and that the person who made request was authorised to do so. They check that the address given in the application matches the address of that organisation in official public records.
This gives the user increased confidence that the data being sent is being received by the organisation in question, and not an imposter.
OV SSL certificates are issued within a few days, due to the identity checks being carried out.
Extended validation certificates (EV SSL)
EV SSL goes even further, with extremely stringent identity checks, beyond those applied to OV SSL requests. For example, there will be paperwork to complete by the requesting organisation, and stringent audit checks to completely rule out the possibility of an imposter requesting the certificate. Only approved CAs, who have themselves been audited and qualified, can issue EV SSL.
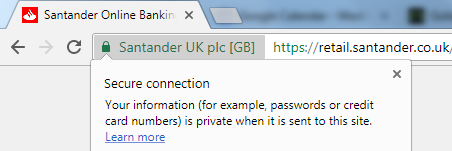
When an EV SSL is in place, the name of the organisation is shown next to the padlock icon in a web browser. This is the only type of SSL certificate that can display the organisation name. A visitor can be sure that the name displayed is truly the organisation they are sending data to. This type of certificate must be used in online banking or the input of credit card numbers.
Issuing EV SSL certificates can take several weeks, due to the stringent checks needed.
Do you need to secure your website with an SSL certificate? We can help!
